When I was in the security group, we found many programmers don’t know how to handle, or don’t have the awareness of Nginx’s security. We found many exploitations or cases of sensitive data was pulled from web servers by attackers.
Here I will list some configurations for Nginx’s Security. Please do adjustments to these configurations according to your actual requirements.

Forbidden any sensitive request path
Many source codes are using Git as version control tools. The directory .git will contains all the metadata of codebase, including some secrets, etc. Expose it to the public will make your codebase downable for attackers:
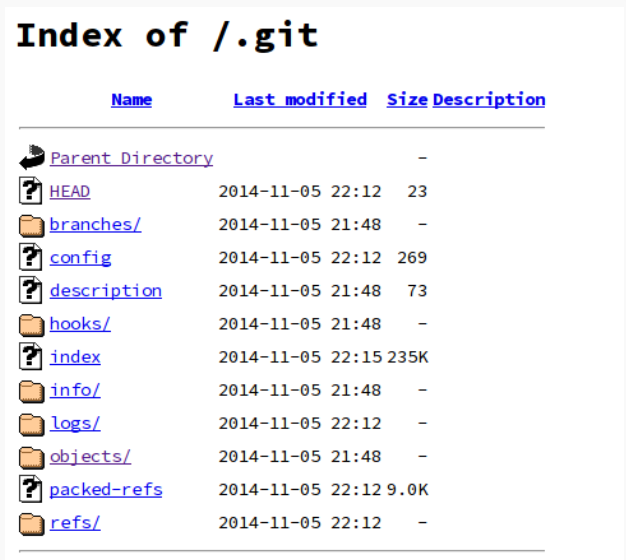
So we need to disable the .git related request routes.
|
Forbidden unnecessary HTTP request methods
The most commonly used HTTP request methods are GET, POST, HEAD. We should return 444 for any other unused methods.
|
Add request rate limiting
Rate limiting will block many malicious requests, and it is also a frequently used tool to defend against network and application-level DDoS attacks against websites.
We can add the maximum request limit for a single IP.
|
Add HTTPS for your service
If you are deploying a non-company project, Let’s encrypt will be enough for personal usage. And remember to redirect all non-HTTPS requests to HTTPS with 301.
|
Enable SELinux
SELiunux stands for Security-Enhanced Linux, it is a Linux kernel security module that provides a mechanism for supporting access control security policies, including mandatory access controls (MAC). It can prevent several attacks before your system being hacked.
Install it on Ubuntu:
|
Clickjacking Attack
Clickjacking attack will cause users to unwittingly download malware, visit malicious web pages, provide credentials or sensitive information.
We can inject X-FRAME-OPTIONS in HTTP Header to prevent a clickjacking attack(Even this can be bypassed in some ways). This is achieved by adding below in nginx.conf file
|
Above header will instruct a browser to load the resources ONLY from the same origin.
X-XSS Protection
Inject HTTP Header with X-XSS protection to mitigate Cross-Site scripting attack. Modify nginx.conf file to add the following
|
Save the configuration file and restart Nginx. You can use the Headers Test tool to verify after implementation.
You may also be interested in implementing OWASP recommended secure headers which are explained here.
References
Mastering NGINX Second Edition is an excellent reference book for the introduction of Nginx.
Join my Email List for more insights, It's Free!😋
